SoftPOS and Snake Oil

Half of all innovation is just talking about it. The more innovative your idea or product is, the more you need to work at creating the awareness and hype that will fuel the demand for your product. Along with the hype, there is usually a healthy amount of ‘smoke and mirrors’ to prove the innovation is real. In the software industry, it is common to see teams hack together a functional proof of concept and then fill in the gaps by promising the rest to customers. Once you have won the customer’s commitment, the real work begins. The complexity of your innovation is usually only discovered after making that first sale. This is most likely why most ground-breaking software projects run late, or even fail. The complexity is not always technical, it could be related to ease of use (UX), compliance, trust, or other soft factors.
Good teams who are passionate about their innovation somehow work their magic and deliver on their promises. But there are also the ones to adopt the ‘fake it till you make it’ approach, and in the long run they either succeed through luck or die (Theranos).
Point of Sale (POS)
You already know about Point of Sale (POS) terminals – those clunky payment devices that you have been mag-swiping or inserting your card into for almost two decades. Recently, contactless payments have become the preferred mode of payment, so now you simply tap your card on the POS terminal to make a payment. Love them or hate them, POS terminals are an essential part of any cashless society. Hardware POS terminals protect sensitive card information (and of course your PIN), until now there was no other secure way to handle that payment data. Your card information needed to be encrypted by a trusted payment device that the Bank commissioned and issued to the merchant.
As technology rapidly advances, more physical items are being dematerialised and replaced by their software equivalents. Just think about calculators, map books, torches, cameras, and many others – these physical items have all been displaced by software applications – all on your mobile phone.
POS terminals are just another casualty of dematerialisation.
Enter SoftPOS
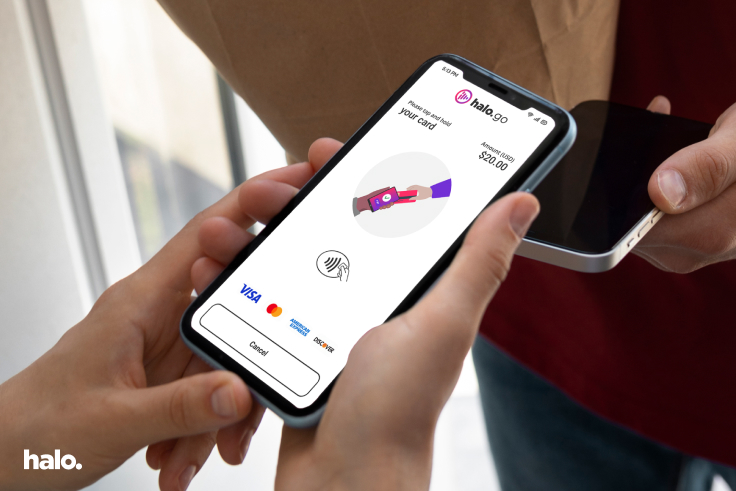
SoftPOS has emerged as the digital successor for physical POS terminals. No additional hardware is required and it works on any Android-based mobile phone. Instead of the payment card being inserted into the POS device, the card is simply tapped on the mobile phone and the App takes care of the rest. This is a contactless payment and uses the same technology that the physical POS terminals use - the device and the card communicate using radio frequencies known as near-field communication (NFC). Most mobile phones have NFC as a standard feature now, even at the entry level class of Android phones.
SoftPOS solves many pain points for different stakeholders in the payment ecosystem. Banks no longer need to manage stock levels of physical devices; they don’t need to maintain devices or offer replacement units when one is faulty. For merchants, they no longer need to pay fees upfront for devices, costly monthly rental fees, and best of all, they don’t need to wait for hardware to be delivered to them before they can start trading. With SoftPOS, its instantly available and can be used anywhere and anytime.
This is considered as incremental innovation but will certainly disrupt the payment industry. SoftPOS provides the potential to scale globally at low costs and can be integrated with any other software applications easily, enhancing the experience for banks, merchants, and consumers.
Building software is easy
There is a common misperception that building software is cheap and easy. Everyone believes they can develop an App quickly, the sheer volume and variety of Apps in the App Store fuels this belief. While coding an App is relatively simple to do these days, building secure software is quite the opposite. Protecting your intellectual property and ensuring your user’s personal data is safeguarded is no easy feat. Malicious actors (let’s call them hackers) from around the world can easily reverse engineer your App and exploit vulnerabilities in the code. Keeping ahead of these hackers is not easy and the proliferation of ransomware and the frequency of data breaches demonstrate how active these hackers are. If you are not practising a security-first approach in your application and software development lifecycle, you will most likely become a victim of an exploit or breach.
When building a payment App, security is paramount and non-negotiable. SoftPOS aims to replace physical POS terminals, so many layers of security are required to ensure the software is on par with, or better than what we have today in POS terminals.
Securing a payment App involves numerous health checks of the mobile device (rooting checks, attestation), it must be resistant to code analysis (reverse engineering), employ the best encryption techniques, and communicate securely with the backend. Additionally, security needs to span across mobile Apps, cloud hosted services, access policies, data protection, documentation and even communication with external parties. Building secure software is not done after the fact as an annual compliance checkpoint, it must be practised every day and people should be passionate about it.
Security is costly, high effort and requires continuous improvement.
Beware the snake oil salesman
Purveyors of SoftPOS are quick to tell their customers that their solution provides everything that the customer needs to accept contactless payments. While their promises may be true at a functional level; their software allows for the basic NFC communication - but it lacks the most critical security components. Much the same way that Clark Stanley’s Snake Oil Liniment was falsely touted as a miracle cure, beware of anyone telling you they can solve all your SoftPOS requirements with their product.
Many SoftPOS vendors have come from the traditional POS world and are simply repackaging their legacy software for use on Android. This low-road approach drives early sales with promises of rapid time to market; but ultimately exposes them further down the track when independent laboratories perform security evaluations. Since their software previously relied on the inherent security features of the POS hardware, there are many gaps that need to be filled. Customers only discover later that they need to fill these gaps on their own.
We have heard from many customers looking to switch SoftPOS providers because the solution they were sold simply does not measure up on the security side. The net effect is that the customer spends months hardening the security of their App and incur thousands of dollars by repeating lab evaluations.
There is no single elixir for SoftPOS, it takes time and requires mobile security experts.
Check what’s in the box
Before selecting a SoftPOS vendor, be sure to analyse what they are really offering you. Is it just a repacked L2 payment kernel, or is it more than that?
Ask the tough questions about security; what credentials the vendor has around cloud and mobile expertise, how much real experience have they got with cryptography, has the solution been tested at scale, and are they prepared to disclose the vulnerabilities and findings from the lab’s evaluation.
If they offer software-based PIN entry – how have they ensured the PIN entry is isolated and adequately protected in memory from other Apps. What pinblock formats are used and how has point-to-point encrypting been implemented.
Don’t just kick the tyres – you must critically evaluate their software and if in doubt, solicit independent opinions from PCI Recognised Labs.