Why SoftPOS Vendors are Embracing Zimperium's Key Protection

The short answer is to prevent on-device payment fraud.
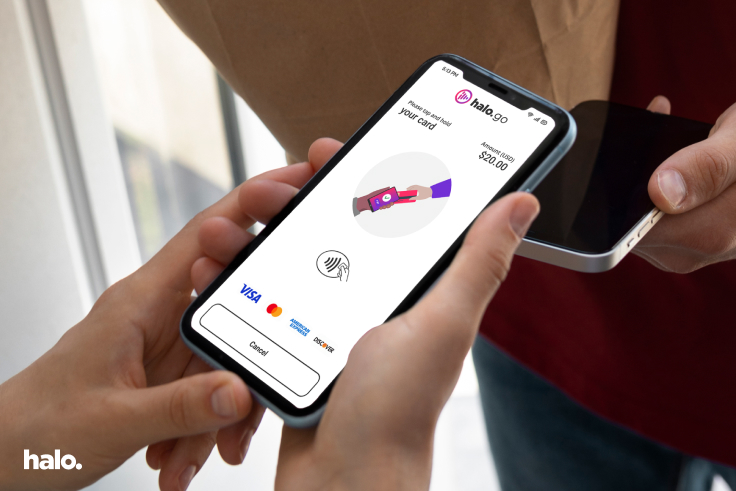
Fraud protection is any SoftPOS provider's primary responsibility. It is also a significant reason why it is such a specialist environment and why there are very few established and approved market players. Consumers and merchants have become very used to "Contactless" or "Tap to Pay" transactions due to their undeniable convenience. The widespread adoption of this payment method is because merchants and consumers inherently trust the underlying specialized mobile point-of-sale hardware. But these specialized terminals cost merchants thousands of dollars annually to acquire and maintain. The future of payments is quickly moving away from specialized POS (Point Of Sale) hardware and racing towards Consumer-Off-The-Shelf (COTS) mobile devices.
Today's specialized hardware primarily relies on an EMV Level 1 (L1) certification. Most SoftPOS solutions in the market solely rely on encryption for security. But encryption is focused on confidentiality. And choosing a robust encryption algorithm and key size is not sufficient if you do not protect your keys. Hackers today are breaking into systems and software by stealing keys rather than breaking the algorithm.
At Halo Dot, our goal is to help consumers and merchants feel safe and trust us to secure their card data on the new generation of COTS devices.
Our SoftPOS solutions attain EMV Level 2 (L2) certification just like a hardware vendor. Since the SoftPOS application runs on COTS devices, they do not require EMV Level 1 (L1) certification to accept card payments.
When we submit our SoftPOS application to the PCI (Payment Card Industry) Recognized Labs for security evaluations, we demonstrate that we have taken all the necessary steps and employed the best security techniques. This is critical to gain the Card Schemes and PCI's confidence that the applications using ourSoftPOS application are well protected from attackers. We have chosen to use Zimperium's enterprise-grade Mobile Application Security Suite (MAPS) to achieve these stringent security goals.
By leveraging Zimperium's white-box cryptography (zKeyBox), we ensure that attackers cannot exploit or instrument the application to locate and exfiltrate sensitive material (cryptographic keys or cardholder data). White-box cryptography ensures that the implementation of cryptographic algorithms is secure even if the attacker controls the device and the execution environment. The solution allows us to hide and protect cryptographic keys so that they are never revealed in plain text — even during the execution of cryptographic algorithms.
Zimperium's Application Shielding solution (zShield) adds another layer of protection by preventing our SoftPOS application from being reverse-engineered and cloned.
With such layered security in place, it becomes incredibly challenging for attackers to compromise our code and attempt to commit payment fraud. This security model also allows us to build trust early with our global customers, prospects, and partners.
Zimperium's industry-leading MAPS solution allows us to deliver our SoftPOS application and Software Development Kit (SDK) to our customers at the best price point in a hyper-competitive and rapidly evolving SoftPOS space. Merchants will continue to be very cost-conscious and SoftPOS is intended to drive down the cost of payment acceptance and increase financial inclusion.